Grey hat hackers Gray hat hackers sit someplace concerning the good along with the undesirable guys. Unlike black hat hackers, they make an effort to violate specifications and rules but devoid of intending to do damage or achieve economically.
So make your passwords extensive and complicated, avoid utilizing the exact a single for different accounts, and rather utilize a password supervisor. Since the price of even one hacked email account can rain disaster down on you.
In 2013, Yahoo encountered two hacking incidents that resulted in a single of the most important facts breaches in heritage, impacting about three billion person accounts. The breach was executed by 4 Russian brokers which were recruited via a hacker-for-use plan.
Some newbie programmers merely hack for enjoyable or to find out or gain notoriety for breaching difficult targets. For instance, the increase of generative AI has fueled a surge of hobbyist AI hackers who experiment with jailbreaking AI types to generate them do new items.
There’s even another group of cybercriminals: the hacker that's politically or socially inspired for many cause. These hacker-activists, or “hacktivists,” try to aim general public focus on an issue by garnering unflattering interest to the concentrate on—normally by creating delicate information and facts general public.
Malicious actors can, and infrequently do, use hacking methods to begin cyberattacks—for instance, someone exploiting a technique vulnerability to break into a community to plant ransomware.
Download from initially-get together resources Only download applications or program from dependable companies and 1st-celebration resources. Downloading content material from mysterious sources indicates end users will not absolutely know very well what These are accessing, and the program could be infected with malware, viruses, or Trojans.
Anyone can disguise their identity on social networking, dating platforms or other websites. In 2019, the Pentagon warned about a growing number of impersonator accounts on Twitter that hijacked the identification of Maritime Gen.
How to proceed: By no means deliver dollars to another person you don’t know. If you think that you built a payment to your scammer, Speak to your financial institution or the business you accustomed to deliver The cash right away and notify them that there may possibly are an unauthorized transaction.
ATM Equipment – Lender ATMs also are vulnerable targets to hackers enthusiastic by fiscal incentives, as a lot of ATMs usually work on outdated software and will be linked to an unsecured community. Flaws in card reader technological know-how will also be employed as a method of cyber hacking.
Contact click here the business or financial institution that issued the bank card or debit card. Explain to them it had been a fraudulent charge. Inquire them to reverse the transaction and give you your a refund.
Con artists use cash and wire transfers to steal people’s funds. If a person you don’t know asks you to send income to them—even when they say They're from the governing administration agency—it should be a purple flag.
identified that companies that closely invest in AI and automation for cybersecurity can lower the expense of a median breach by USD 1.88 million. In addition they establish and comprise breaches 100 days quicker than organizations that don’t invest in AI and automation.
Learn more about your rights as being a purchaser and how to location and keep away from scams. Locate the means you should understand how client defense regulation impacts your business.
 Yasmine Bleeth Then & Now!
Yasmine Bleeth Then & Now!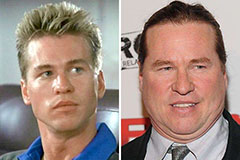 Val Kilmer Then & Now!
Val Kilmer Then & Now! Seth Green Then & Now!
Seth Green Then & Now! Gia Lopez Then & Now!
Gia Lopez Then & Now! Susan Dey Then & Now!
Susan Dey Then & Now!